Your biggest workforce isn’t human.
By Rob Ojevaar, Founder & CEO of Booleans

The 82:1 Ratio: a C-Level Mandate to Own the Invisible Workforce
When we reflect on the modern enterprise landscape, specifically the highly innovative business, we recognize a predictable, recurring architectural pattern. It is not a failure of talent, but a byproduct of velocity.
We recall a specific scenario we have observed at numerous global innovators: a Lead Cloud Architect is facing a critical deployment error that threatens a high-stakes AI deployment. The Friday launch is non-negotiable, but the formal governance process for service provisioning takes three days.
In that defining moment, developer autonomy wins. The fix is non-standard. The architect creates a service account, generates a long-lived API key, and grants it full administrative privileges to ensure no ‘Permission Denied’ errors stall the launch. The secret is stored in the personal password vault, the deployment is a success, and the business moves forward.
But the architectural footprint remains long after the architect is gone. We see this “Noble Shadow” buried under a mountain of what Gartner defines as “Identity Debt.”
The High Cost of Identity Debt (and the rise of AI)
Identity Debt compounds when you layer Non-Human Identity (NHI) sprawl on top of existing IAM silos, Workforce, Customer (CIAM), and Cloud-Native. These systems often speak different languages: SAML for legacy and enterprise SSO, OIDC for modern application identities, and Cloud IAM Roles for governing infrastructure access. The result is a failure to provide a single truth.
We recently worked with an organization that discovered an 82:1 ratio (Q1 2026) of these invisible identities to humans. While the corporate directory listed 1000 employees, the digital infrastructure was powering 85.000 active identities holding keys to the kingdom.
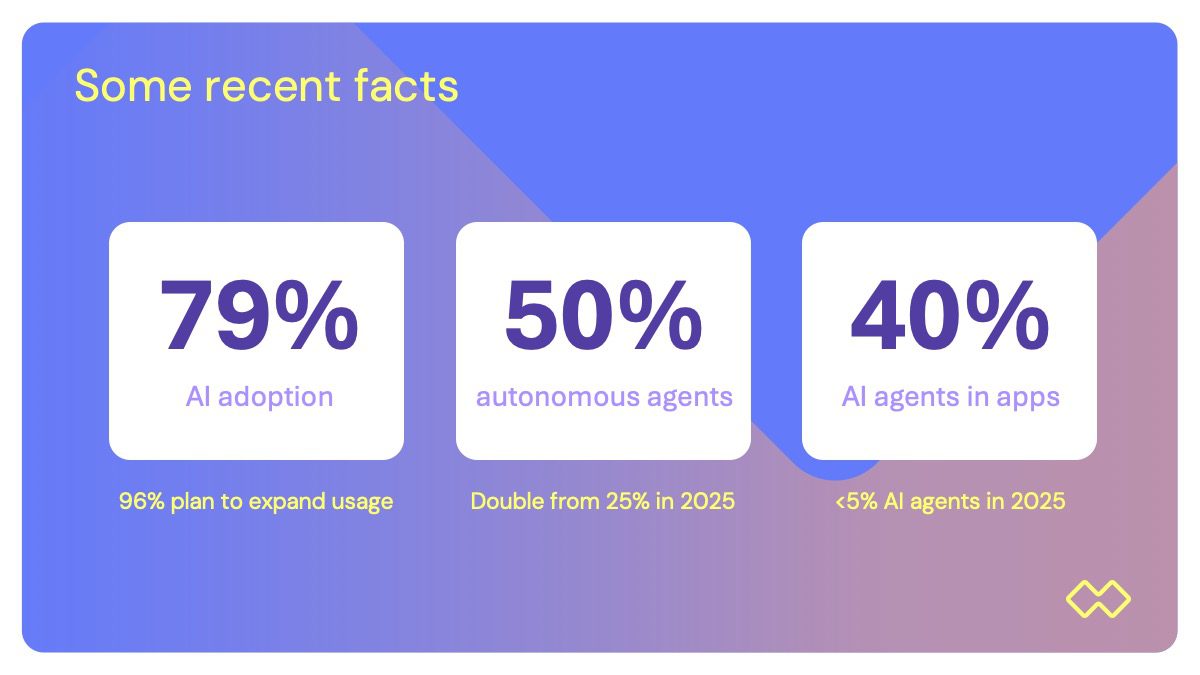
For leadership, this debt is already an existential risk. If you do not resolve this foundational sprawl now, your upcoming “AI Agent” rollout will be a disaster. AI agents are autonomous, dynamic, and require deep system access. Without a clean identity fabric, you aren’t just deploying innovation; you are deploying unmanaged, over-privileged actors into a landscape where 50% of new cloud vaults are already created in the shadows.
The Ownership Vacuum and the Crisis
Consider what happens eighteen months down the road. An audit detects a surge in egress traffic from an Azure storage account. A routine check.
We have seen this moment become a crisis because of the Ownership Vacuum. The audit logs will show a generic “Service Role” accessing data. But when the CISO attempts to trace this back, they hit a wall. That role was triggered by a CI/CD pipeline, authenticated by a secret in Azure Key Vault, which was originally provisioned by an employee who left the company a year ago.
This vacuum is made even more impossible to manage by the rise of ephemeral tokens. When an identity exists for only seconds to perform a task and then vanishes, traditional logging is useless.
Without the ability to link these short-lived “ghost” tokens back to a human owner in real-time, lateral movement becomes invisible and stopping it requires days of expert intervention.
The Booleans Guidance: From Sprint to Strategy
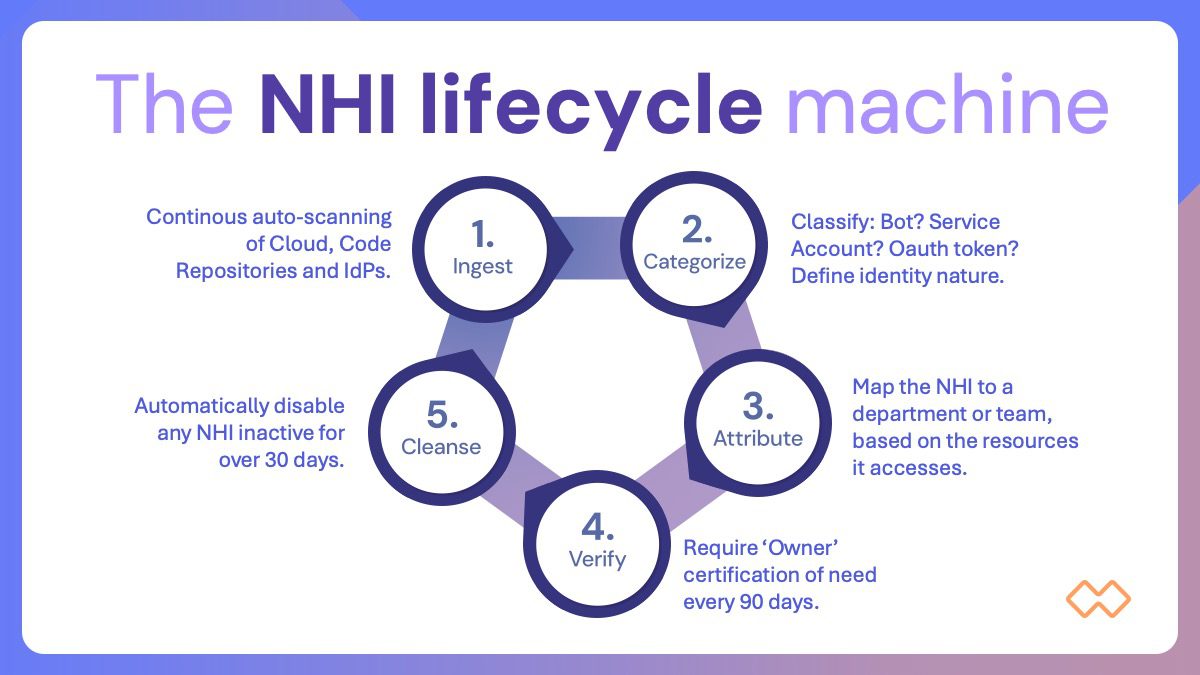
The lesson from this architectural drift is that you cannot solve a 2026 problem with a 2010 mindset. While our 90-day NHI Governance Sprint provides the immediate “kill-switches” and visibility required to secure your environment today, it also establishes the foundation for three levels of long-term strategic guidance:
- Workload Identity Federation: Stop “storing” secrets. We use the sprint to identify high-risk static keys and pilot a move toward a “secretless” architecture where cloud providers “trust” your directory identity directly via short-lived tokens.
- Machine Identity Management (MIM): Treat NHIs as first-class citizens. We help you bake NHI governance into your corporate directory’s existing JML (Joiner-Mover-Leaver) process. If there is no human heartbeat attached to an identity, that identity is challenged or removed.
- Bridge the Silos with Orchestration: Eliminate the “Identity Fabric” crisis by implementing an abstraction layer. This allows your security team to enforce one consistent policy across all your cloud environments and identity providers from a single pane of glass.
Own It and Uncover the Invisible
The invisible workforce is growing by 44% year-over-year. These are not passive “accounts”; they are autonomous agents that can act, decide, and trigger workflows.
If your IAM program cannot map the cross-platform permissions of the 85 machine identities operating behind every single employee, you aren’t just at risk; you are operating on borrowed time.
For any CIO or CISO, the mandate is clear: It is time to step up to own it and uncover the invisible!
Ready to bring visibility and governance to your invisible workforce?
Let’s meet